It’s official: Apple will be providing a full SDK for iPhone and iPod Touch developers in February ’08.
Nice move Steve! All I want is to keep my eBook reader.
It’s official: Apple will be providing a full SDK for iPhone and iPod Touch developers in February ’08.
Nice move Steve! All I want is to keep my eBook reader.
Hot damn! Apple is dropping the price of their iTunes Plus tracks from $1.29 to $.99, probably in direct response to Amazon’s MP3 store, which also offers DRM-free tracks at $.89 to $.99. I know I first check Amazon before getting something from iTunes – with no DRM and a cheaper price, it’s a no-brainer.
At least now the playing field is leveled slightly.
Last night I finally got 3rd party apps running on the phone again after the disastrous 1.1.1 update. I used Niacin’s TIFF exploit to get write access to the filesystem, and then followed the directions from the iPhone Dev Team (detailed here) to get SSH and AppTapp installed.
It’s still a very manual process, but way easier than the downgrade to 1.0.2 then update to 1.1.1 nonsense. But now I have my eBook reader and IM client running again. Summerboard doesn’t work, and neither does Sketch or Customize(apparently Customize does work, thanks Brian), but for the most part, everything runs just fine. A list of common applications and their compatibility can be found on this iPhone Dev Wiki page.
If you’re going to try this, remember that this doesn’t get you the carrier unlock, just 3rd party apps. Unlocks are still coming, though there have been reports that the IPSF stuff still works. Apparently it was the only software unlock that didn’t brick the iPhone with the 1.1.1 update. Naturally, it costs $60.
Now to wait for the inevitable breakage from Apple’s next update. Sigh. Can’t we all just get along?
Update: Looks like they decrypted the ramdisks now.
Finally – the addictive building game gets an upgrade to a universal binary. The old PPC version ran ok on my Intel box, but some of the more complex bridges got REALLLY SLOW during simulations.
You owe it to yourself to get a copy of this game. Also check out Bridgebuilder-game.com to find tons of pre-built bridges and some nice solutions to the more tricky levels.
Technorati Tags: Bridge Contruction Set, games, os x
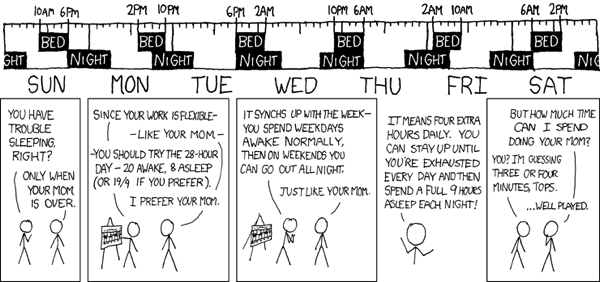
The 28 hour day/week. Courtesy of xkcd.com
It appears that the usefulness of MD5 checksums is finally beginning to wane. This security analysis by Dan Kaminsky gives some frightening details of how to create two files that perform different tasks, but have the same MD5 checksum. Bad news. Now this attack relies on the possession of two specially-computed files that have the same checksum, as detailed by Joux and Wang previously:
For MD5 (and actually a number of popular hashing algorithms, SHA-1 not among them), it is possible to compute particular classes of input data for which subtle changes can be silently introduced without causing apparent changes in the final MD5 hash. Capacity is not huge – of the two 128 byte proof-ofconcept files released by Wang, only six bits differ. But many â€doppelganger†sets can be computed, each of which may be swapped out with the other at no effect to the resultant hash. The sets are two MD5 blocks long. Because it’s possible to compute new blocks on demand, a generic â€antivirus†style colliding block detector isn’t possible. It may be possible to generate a custom weak class detector. The ability to generate colliding datasets exposes a fundamentally new mode of operation for MD5.
Now, you don’t have to start worrying about this immediately. Fully-practical attacks are still over the horizon. However, as Dan’s paper shows us, the horizon may be closer than you think. You may want to read up on SHA-1.
This article from the New Scientist print edition has a small interview with Benoit Mandelbrot. If you don’t know who he is, you need to turn in your Geek Credential card at the door, please. A small excerpt:
Q: Even though most people view it as a beautiful image and ignore the underlying mathematics?
A: That’s right. Yet there is nothing more to this than a simple iterative formula. It is so simple that most children can program their home computers to produce the Mandelbrot set.
I thought that this was pretty funny. When I first got my hands on a C compiler for my lowly Commodore 64, one of the first things I did was to try and build a program to display the Mandelbrot Set. Previously I had taken his book, The Fractal Geometry of Nature out of the library (I later purchased a copy.) I wanted to write some software to generate the set, but my meagre computing resources limited my language selection (let’s see – assembly or BASIC…)
I even wrote a letter to Mr. Mandelbrot on a sheet of notebook paper asking what language he used to write in (among other questions.) He replied, and I still have the letter in my files. It contained a signed hand written note saying he used FORTRAN as his language of choice, and he included some photocopied sheets giving some implementation details and hints. I was 13 at the time, and I was in heaven. Yes, other people may have written letters to pop stars. I wrote to a mathematician working at IBM’s research labs.
But I eventually found a C compiler (Abacus C) and began writing, translating the formulas found in the book into what was, looking back on it, poorly crafted C code. The result? After some debugging and letting my little program run for nine hours, I had a simple monochrome 320×200 representation of the Mandelbrot set on my screen, red on black. Later revisions added the color gradients you see on so many versions of the set, though I was limited here to four colors and this halved the horizontal resolution. I even was able to add a simple zoom function. But with nine hours between selections, I didn’t go very deep.
A few years later I got my first PC, and one of the first things I did was buy Borland’s Turbo C and move over my Mandelbrot program. Somehow, it wasn’t quite the same. I could watch in real time the whole set being generated on the screen. Many more colors available. Zoom was even practical and useful. Just didn’t have the feeling of anticipation that the 1Mhz C64 generated as you watched, pixel by pixel, the set being drawn.
Ah, yes, the good old days.
Here is a great little page that gives a whole pile of small sed scripts for all kinds of random tasks. This is a great quick reference for all those who don’t use sed enough to remember it’s arcane syntax.
If you don’t know what sed is, feel free to ignore this.